It’s no longer a question of if a cyber security attack will hit; but when. Companies need to do everything they can to keep a serious “when” from ever happening. In fact, in today’s digitally dependent world, midsize enterprises across all industries receive hundreds of security alerts daily, of which only a small percentage can be investigated—and only if security teams have the right security tools and staffing levels. The worst part? According to Gartner research, in 2021, only 5% of a midsize enterprise’s IT spend was allocated to security…5%!
Do you see the problem here? SecOps teams at midsize enterprises face an overwhelming amount of cyber threats to monitor with limited resources to address them. They are also hamstrung by siloed network and security tools that don’t share full visibility and data. All of this is being managed by small SecOps teams which leads to burnout and job dissatisfaction. As if those concerns weren’t enough, companies, when compromised, are getting hit with an average cost per data breach of $4 million.1 We are talking about some serious repercussions here.
How do midsize companies fall victim to cyber threats in the first place? Here’s a look at how an attack cycle works from a kill chain perspective:
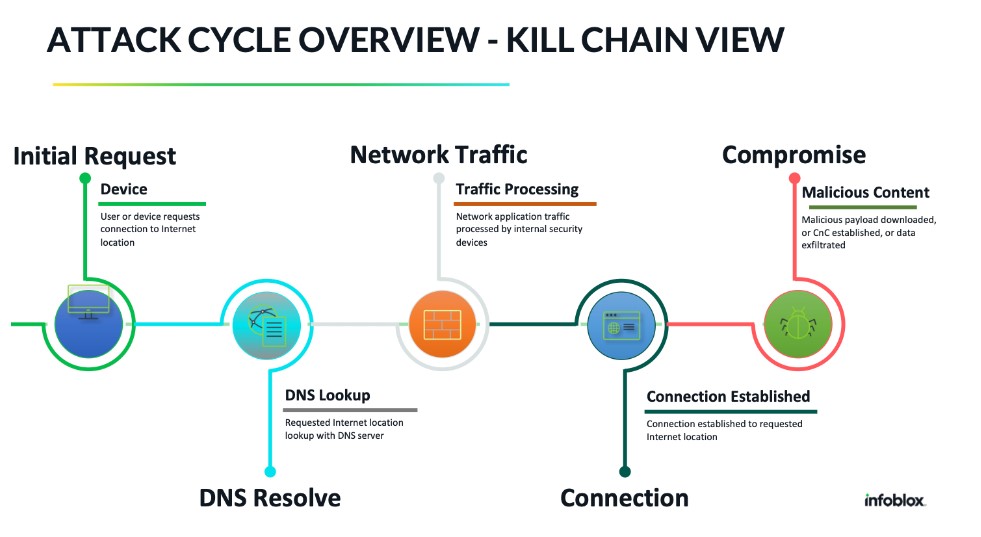
Typically the attacker creates a malicious payload in what’s called the “weaponization stage,” and delivers the payload to a target, often through a spear-phishing email. When a user clicks on the link, the device requests a connection to the Internet location, and the lookup is done via the DNS server. Then, network security devices, such as next-gen firewalls and web gateways, process the traffic and establish the connection. Once the connection is established, the payload is downloaded and executed on the target device. This is how the malware inserts itself into an environment. After creating a foothold, the attacker can now remotely control the device via command and control (C&C), move laterally, and finally carry out their intended goals such as data exfiltration.
What’s a resource-strapped midsized enterprise company to do? The answer is simple, ease the burden on perimeter defenses by utilizing a DNS-based security solution to “shift left,” and stop attacks at the beginning of the attack cycle, not after, when it is too late.
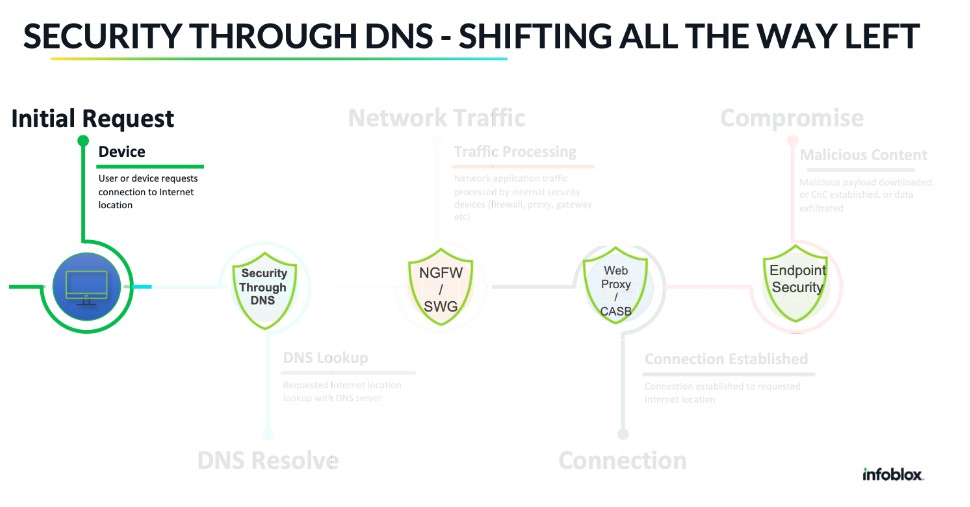
The smartest way to disrupt the entire kill chain is to shut it down at the very outset—at the point a device attempting to reach a malicious destination makes the initial lookup request to a DNS server. Using DNS as a first line of defense prevents resolution to a malicious domain at the beginning of the connection path—before those requests even reach next-gen firewalls, web proxies, and gateways. In cybersecurity, this concept is known as “shifting left,” moving defense measures to the left in the connection path.
Leveraging DNS for cybersecurity is critical when you consider that 92 percent of cyber attacks rely on DNS in their execution, according to the United States National Security Agency (NSA). And yet, according to IDC, only 42 percent of organizations are protected at the DNS layer.
There’s no doubt DNS is an essential network service. It is required for every device, including managed and unmanaged devices, and it spans the entire organization. As you can see in the above graphic, DNS-based security stops potential attacks sooner, taking the burden off security tools further down the line. As such, it is a vital component of defense-in-depth cybersecurity. Plus, DNS security can also include proactive machine learning (ML)-based threat hunting, which exposes DNS-based threats other security solutions would miss. This capability frees each security tool to do what it is designed to do in the most efficient way possible.
But let’s back it up a moment and discuss what a defense-in-depth strategy is and why it matters to midsized enterprises.
Defense in Depth and DNS
If yours is a midsize enterprise, implementing defense in depth is crucial for protecting against cyber threats. As your business grows, so do the risks you face. Hackers and cybercriminals often target midsize enterprises for two reasons. First, because they have valuable data. And second, because these enterprises often lack the security protections larger organizations can deploy. As such, hackers view midsized enterprises as “easy” targets.
Defense in depth is a cybersecurity strategy that uses multiple layers of security to protect against cyber threats. The idea is to combine different security measures to make it more difficult for attackers to breach your network and steal your data. Traditionally, security layers often include firewalls, intrusion detection and prevention systems (IDS/IPS), antivirus software, etc. I’m advocating for the inclusion of an additional security layer to your security stack: DNS detection and response. This security layer does what other layers cannot—it blocks a wide range of malware, ransomware, APTs, and other cyber threats from the start, at the initial DNS query. Moreover, it automatically bolsters protection for midsized organizations with limited staff, budget, and security expertise.
Defenses that make use of DNS detection and response are readily deployable. If you have a network, you already have DNS in place. Since every device on your network relies on your DNS infrastructure, why not use DNS-layer security to deepen your defense in depth with every device interaction? Doing so imparts the following benefits:
- Reduced load on downstream security devices—Increase capacity, extend life, and improve ROI on a manageable set of security tools.
- Increase staff productivity—DNS Detection and Response approaches provide robust capabilities to speed up response to threats and make SecOps more productive.
- Reduce security alerts to SecOps and SIEMs—Lower SIEM costs while increasing SecOps efficiency with fewer alerts and false positives
- Protect all, not just some, devices—Every device uses DNS to resolve destinations before communicating, thus blocking malicious threats before they have a chance to enter the network.
- Simplify Regulatory Compliance and Audits—DNS-layer security fills existing gaps in risk assessment, security monitoring, and detection processes that are critical functions in meeting compliance and audit requirements.
Don’t Forget About Employee Training
Adding DNS detection and response to your defense-in-depth strategy is a significant step forward, but security awareness training is another component to address. Employees can play a role in an organization’s security plan. Educating your employees about cybersecurity best practices is essential to reduce the risk of human error. Of course, we are human, and we all make mistakes. Having a baseline awareness of threats can help alleviate common errors.
To implement an employee cybersecurity education program:
- Develop training that covers topics such as password security, phishing, and social engineering.
- Conduct regular training sessions, or at least send email or Slack summaries, to keep your employees up-to-date on the latest security threats and best practices.
- Encourage your employees to report any security incidents or suspicious activity before they click.
- Test your employees’ knowledge of cybersecurity best practices through simulated phishing attacks.
Again, when dealing with humans, mistakes are inevitable, even with security training. With DNS security as the first step in a defense-in-depth strategy, you can already feel some of the pressure on your SecOps team melting away.
Now’s the Time for Midsize Enterprises to Act
As a midsized enterprise, you are in the crosshairs of cybercriminals who consider you an easy target. Prove them wrong! Using defense in depth, including DNS detection and response, midsize enterprises can reduce their risk of cyberattacks and protect their valuable network and data without negatively impacting costs, staff, and other resources. Foundational DNS detection and response solutions, like BloxOne® Threat Defense, work hand-in-hand with your other layered defenses. When combined with easy-to-understand employee security education, you are on the right track to creating a comprehensive strategy that addresses today’s most worrisome cyber threats—and potentially stopping a $4M breach from happening on your watch.
1. Full Report: https://www.ibm.com/security/data-breach; Summary: https://newsroom.ibm.com/2022-07-27-IBM-Report-Consumers-Pay-the-Price-as-Data-Breach-Costs-Reach-All-Time-High