Infoblox is pleased to publish our 2023 Healthcare Cyber Trend Research Report. This report includes analysis of the major healthcare data breaches directly attributed to cyberattacks within the United States during calendar year 2022. We also include data from 2016 through 2022. Because timely information on cyber threats is vital to protect the healthcare user community, we share our research and insight into cyberattack trends and events that continue to impact the healthcare industry.
Healthcare institutions seek the cost and technology advantages of digital transformation. Digital transformation, in turn, will enable the healthcare industry to reduce costs, improve patient outcomes and deliver many additional benefits. Unfortunately, the rapid digital transformation continues to expand the attack surface available to threat actors.
New research data shows us that in 2022 there were 546 major data breaches due to Hacking/IT in 2022, which reflects a 4 percent increase over the 521 major data breaches due to Hacking/IT reported by healthcare institutions in 2021. These numbers have been growing steadily higher for over five years.
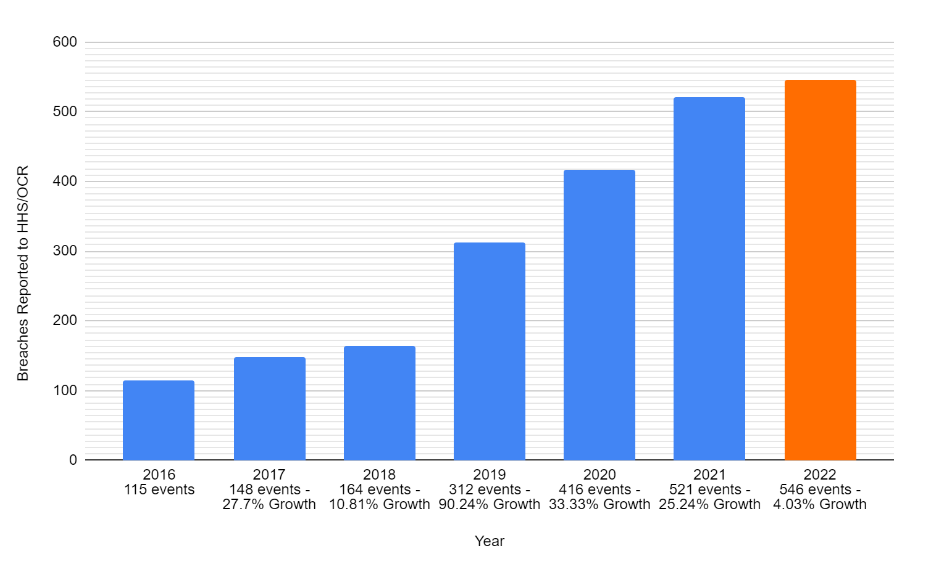
The above chart reflects the number of events reported and attributed specifically to Hacking/IT in each of the years shown – not data breaches due to other causes.
While overall data breach counts available in the HHS/OCR database of incidents might appear to have gone down a very small bit in 2022, the data that reflects this reduction might include incidents where a box of 500+ patient files was left in a parked car, and stolen. That gross count of data breaches includes any possible cause, including many that have nothing to do with malicious cyber activity. That could be misleading for security, information technology, and network operations teams that need to be alert to cyber threats.
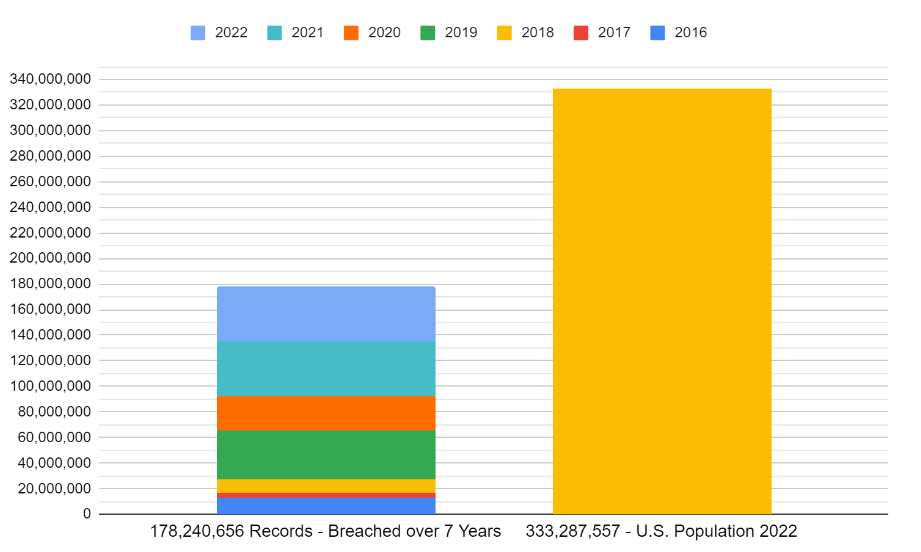
In context, from 2016 through 2022, the total healthcare data stolen in the U.S. due to Hacking/IT included 178,240,656 data records. This number represents approximately 53 percent of the estimated U.S. population of 333,287,557 per the U.S. Census Bureau. There is likely some overlap, with some individuals impacted by multiple PHI data theft incidents. But the number is still massive. During 2022, U.S. healthcare organizations experienced data breaches due to Hacking/IT that impacted 43,387,155 patient records.
Let’s be clear – hacking and malicious cyber activity is front and center when it comes to the data breaches that in some cases severely impacted healthcare institutions in 2022.
These numbers are quite astounding.
Consider that this includes none of the likely thousands of additional Hacking/IT data breaches that impacted fewer than 500 patient records—there is no authoritative source yet for this data. How big would the seven years total be if this data were included?
We expect that our healthcare institutions will remain under continued attack by organized crime and potentially nation-states. They are intent on extorting money through ransomware and leveraging a growing set of malware, phishing and social engineering. Given the data, we don’t expect this trend to reverse anytime soon.
The responsible healthcare organization reports major data breaches under the requirements of the Health Insurance Portability and Accountability Act of 1996 (HIPAA) Breach Notification Rule (CFR 164.400-414), which requires HIPAA-covered healthcare entities and business associates to provide notification following a breach of unsecured protected health information (PHI). Our research data documents statistics about breaches that we refer to as major. These major breaches are found within the U.S. Department of Health & Human Services Office of Civil Rights (HHS/OCR) reporting as attributed to Hacking/IT and impacting more than 500 individuals as reported by the covered entity.
DNS Security Is Essential
DNS security provides visibility into the large volumes of DNS requests made both to and from a healthcare institution’s networks. Visibility allows your cyber defenders to identify and block potentially malicious DNS requests that could be part of an attack’s lifecycle. DNS requests can help your security teams specifically determine if any device within your networks is communicating with known malicious domains. Once identified, DNS security and your cyber defense ecosystem can block these requests to prevent the download of additional malicious code or attempts to steal PHI and other sensitive data from your networks.
Most traditional security controls have limited to no visibility because their inspection of DNS is very minimal. Foundational security with DNS controls are the key to having necessary visibility to identify and mitigate most modern threats. The policies in these security controls often default to allowing all DNS traffic.
Threat intelligence providers might be able to detect active campaigns using malicious domains on the Internet. Timeliness is always the issue because this list of domains changes constantly. DNS tunneling detection, when it exists in legacy products, is primarily based on threat intelligence or signatures for known tunnels. This is not sufficient, as there may be malicious domains that don’t show up in any threat intelligence feed.
As we noted in previous reports, Infoblox has spent years developing and refining machine-learning analytics to detect new threats, sometimes referred to as zero-day threats. We have deployed machine-learning models that allow our platforms to detect these advanced threats that could be exfiltrating data, including to destinations that may not be deemed malicious in threat intelligence feeds. These algorithms, which are part of Threat Insight in Infoblox’s BloxOne® Threat Defense solution, have allowed us to detect data exfiltration across various network deployments.
Many legitimate, benign applications also tunnel data via DNS. Blocking all DNS tunnels is not the solution. Blocking DNS tunnels can often lead to blocking security tools, such as antivirus software, that rely on DNS tunneling to bypass firewalls to update endpoints. Machine learning combined with deep knowledge and experience with DNS give healthcare providers the security controls to protect against zero-day attacks that leverage DNS without blocking legitimate, important applications.
Phishing attacks are a major problem for the healthcare industry. Phishing is a category of cyberattack in which threat actors send fraudulent emails that are designed to appear to be coming from a legitimate source. The goal is to lure people into providing sensitive information, such as login credentials, access to patient records and financial information. By using tools such as DNS Security Extension (DNSSEC), healthcare organizations can authenticate DNS records as coming from a valid and legitimate source.
Malware and ransomware are also frequently used against healthcare institutions. DNS malware protection guards healthcare institutions by identifying and blocking requests that seek to go to known malicious domains. Social engineering may enable attackers to get healthcare clinicians to go to a malicious website, but the DNS security will prevent the malware from being downloaded and executed.
In any scenario, DNS security can add vital defenses to help protect healthcare organizations against threat actor activity. This protection can include preventing and mitigating malware, identifying high risk lookalike domains, phishing and data exfiltration attacks.
Please download your copy of The 2023 Healthcare Cyber Trend Research Report: https://www.infoblox.com/resources/whitepaper/2023-healthcare-cyber-trend-research-report.
For more information about our paid threat intelligence services and products please go to https://www.infoblox.com/products/threat-intelligence/ or reach out directly to our sales team via https://www.infoblox.com/company/contact/.