The biggest problem in cybersecurity today is not figuring out how to prevent the next big attack on the horizon. It’s figuring out how to use the limited time and resources you have to detect the most critical threats fast, before it is too late. Security teams are often overwhelmed with alerts and don’t know how to prioritize and rapidly respond to an intrusion.
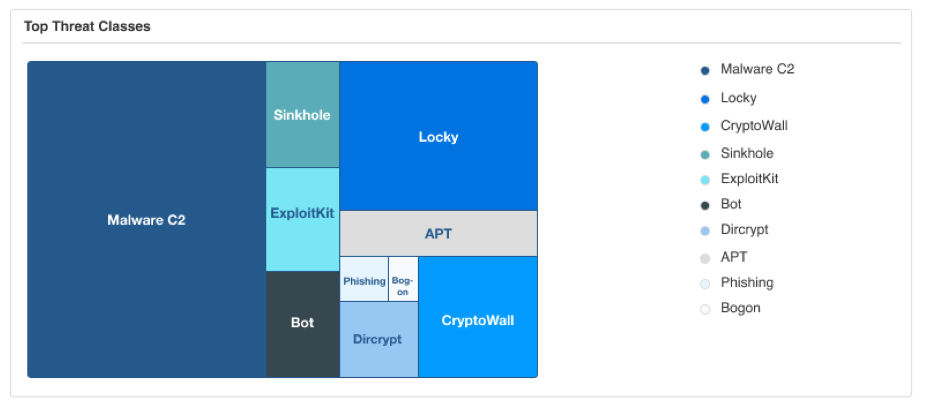
Not every threat is created equal. Understanding damage potential of various types of malware goes a long way in helping security teams focus on high value threats, without getting lost in the noise. It is also equally important to understand the consequences of getting exposed to a particular threat, so that if a user or device is exposed, you can decide whether to prioritize that event over others.
Better information leads to better prioritization
Many threat intelligence providers provide some sort of a threat score that allows security admins to understand the nature of a threat sample. But using a threat score alone doesn’t give you the entire picture. In order to more efficiently prioritize response to threats, you need to be able to answer the following questions:
- Does a particular threat indicator have the potential to inflict severe damage to my network or data if some of my devices and users have been exposed to it? What is the overall risk to the business?
- What is the likelihood that a user is exposed to a threat? If the likelihood is high, what is an acceptable response time to keep the damage to a minimum?
- Are you really confident that the threat classification is accurate? Or are you just chasing things down that are not real threats?
Determining Time to Mitigation (TTM) using Threat, Risk and Confidence Scores from Infoblox
Threat Intelligence from Infoblox helps minimize risk and protect against cyberattacks throughout your security infrastructure with timely, accurate, contextual threat data. The data is curated by Infoblox’s Cyber Intelligence Unit and includes research from Infoblox and more than two dozen threat intelligence partners, including commercial threat intelligence providers, government agencies, the Department of Homeland Security’s Automated Indicator Sharing (AIS) program and universities. Infoblox threat Intelligence is aggregated onto a single platform (known as Threat Intelligence Data Exchange or TIDE) and can be used not just in Infoblox infrastructure, but across other existing security tools in your network like NGFWs, web gateways and SIEM.
One of the ways Infoblox threat intelligence is made actionable is through the availability of three types of scores – threat score, risk score and confidence score – for indicators of compromise (FQDN, IP or URL). These scores are generated using supervised learning models and weighted heuristic scoring models and can be used to determine the time to mitigation (TTM) appropriate for your organization when faced with a security incident.
Threat Score
The threat score describes the severity or level of threat of a given indicator (FQDN, IP or URL). It provides a numeric and qualitative metric for the indicator and takes into account various characteristics such as malware family, top-level domain (TLD), geographic location, autonomous system organization (ASO) and degree of penalization (DOP).
This information allows a security admin to decide how soon to start the mitigation process if a user or device has been exposed to the threat.
Risk Score
The risk score highlights the likelihood that a user could be exposed to a threat or be compromised by interacting with an indicator. It takes into account factors such as detection cost, mitigation time cost, malware family and impact on business services availability. The higher the probability of exposure to a threat, the more urgent it will be to investigate the incident.
Confidence Score
The confidence score represents the level of confidence in the classification a given indicator and takes into account the reliability of sources used to classify a threat.
These scores, which can be used to prioritize and take action on threats, are available in the Infoblox TIDE platform, part of BloxOneTM Threat Defense, a hybrid security solution that uses DNS as a security control point.





