I just finished reading Gartner’s new–and mercifully short—report on using DNS to improve security posture.
It’s encouraging to read Gartner analysts actively supporting DNS as an effective means of preventing, detecting and responding to security threats. Gartner obviously has tremendous reach as an organization, and with luck, this document will bring some organizations around to using DNS for security purposes that have been skeptical or simply slow to adopt until now.
Gartner specifically calls out two issues that Infoblox has tried to highlight for some time:
- The importance of having control over your organization’s DNS resolution. With this control, organizations can prevent its users, software and devices from communicating with malware command-and-control infrastructure and phishing sites, as well as much else. Logs of DNS resolution can be invaluable when analyzing successful compromises and trying to gauge their extent. Passive DNS data can be fed into machine learning algorithms to detect more subtle abuses.
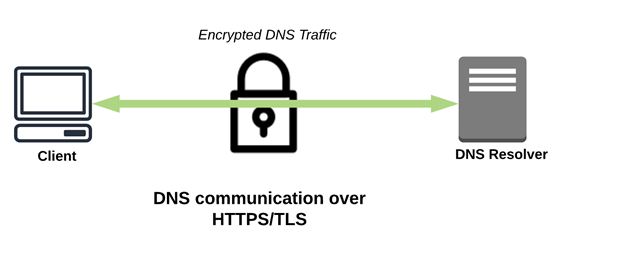
- The threat of certain DNS over HTTPS (DoH) implementations to the previous, as some implementations (I’m looking at you, Firefox) ignore system- and network-derived DNS configuration to use an entirely different set of DNS servers. By allowing this circumvention of their own DNS infrastructure, organizations are not only giving their sensitive, private DNS telemetry to a DNS provider they have no formal relationship with, they’re also foregoing the many benefits that controlling your own DNS infrastructure can provide (see above).
Gartner also mentions the utility of secure, cloud-based DNS services in protecting an increasingly remote workforce. DNS provides an ideal means of preventing corporate-owned devices from accessing hostile Internet resources, and gives an IT organization visibility into user and device activity that they’d otherwise likely lack.
It’s not exactly a summer beach read, but highly recommended nonetheless!
Read more about the Gartner’s latest analyst report »