In April 2023, Infoblox disclosed the discovery of Decoy Dog, a malware toolkit that uses the domain name system (DNS) to communicate. Since then, we have continued our investigation and have gained valuable insights into Decoy Dog’s capabilities and the behaviors of many of its controller domains in the wild. What we found is alarming and mysterious. This article provides a brief overview of our conclusions. Get the full report, including our Decoy Dog YARA rule, here and read the original paper here.
What is Decoy Dog?
Decoy Dog uses DNS to perform command and control (C2). Infoblox was able to discover the malware through anomaly detection algorithms at our BloxOne Threat Defense resolvers. Decoy Dog is based on Pupy, an open-source remote access trojan (RAT), but is far more sophisticated than the pen tester’s tool. Infoblox is currently tracking 21 Decoy Dog controller domains and is actively monitoring DNS for more; these domains appear to be under the control of at least three actors. Throughout this article we use the term Pupy to specifically refer to the Pupy DNS C2 component.

Decoy Dog traffic has increasingly been observed at Infoblox resolvers over the past 12 months. While this traffic looks like Pupy, there are significant differences. It contains new commands and communication protocols, advanced mechanisms to avoid disruption of communications links between the clients and server, and significant rewrites of core communication modules. Surprisingly, Decoy Dog was only detected through its DNS traffic and no victims have yet been identified, adding to the mystery of this malware.
Decoy Dog Activity
The first Decoy Dog controller observed was cbox4.ignorelist[.]com. It became operational in late March to early April of 2022. Shortly after that, a second controller, claudfront[.]net, came online in May 2022 with a different set of characteristics, indicating that it may be operated by a different threat actor. A third controller domain, allowlisted[.]net, was registered in July 2022, but was strategically aged and didn’t become active until September 2022. It shares many similarities with claudfront[.]net, leading us to believe that they are likely operated by the same actor. Two more controllers, hsps[.]cc and ads-tm-glb[.]click, were later created with a similar set of characteristics that were distinct from previous controllers, indicating a third threat actor had also started using Decoy Dog.
Infoblox is tracking other Decoy Dog domains beyond these we mentioned; those may be operated by additional actors. The past six months have shown a steady rise in registrations of domains that are used as Decoy Dog controllers; some of them were registered immediately following Infoblox’s initial disclosure on LinkedIn (see Figure 1).
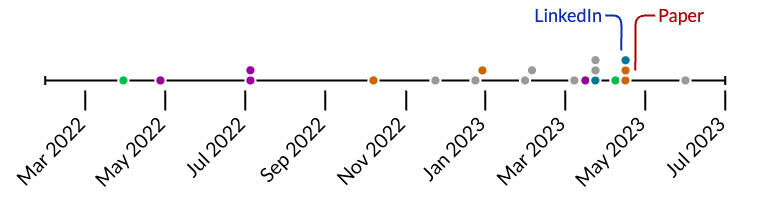
Figure 1. Domain registration dates for known Decoy Dog controllers are shown. Domains with the same presumed actor share a color.
Infoblox created a statistical algorithm to estimate the number of active clients at any time, based on DNS queries. Figure 2 shows this for some of the most active Decoy Dog controller domains dating back to March 2022. The controller with the highest volume to date, cbox4.ignorelist[.]com, was deactivated shortly after our initial disclosure of domains on LinkedIn. We also designed algorithms to determine that others, such as hsps[.]cc and ads-tm-glb[.]click, moved their clients to new domains, nsdps[.]cc and j2update[.]cc, respectively. These new controllers are now geofenced and only respond to requests from specific regions, including Russia. Lastly, the two controllers claudfront[.]net and allowlisted[.]net, both hosted on Russian service providers, continued their operations after the publication of our report, but did make a change to the response for “ping” domain queries.
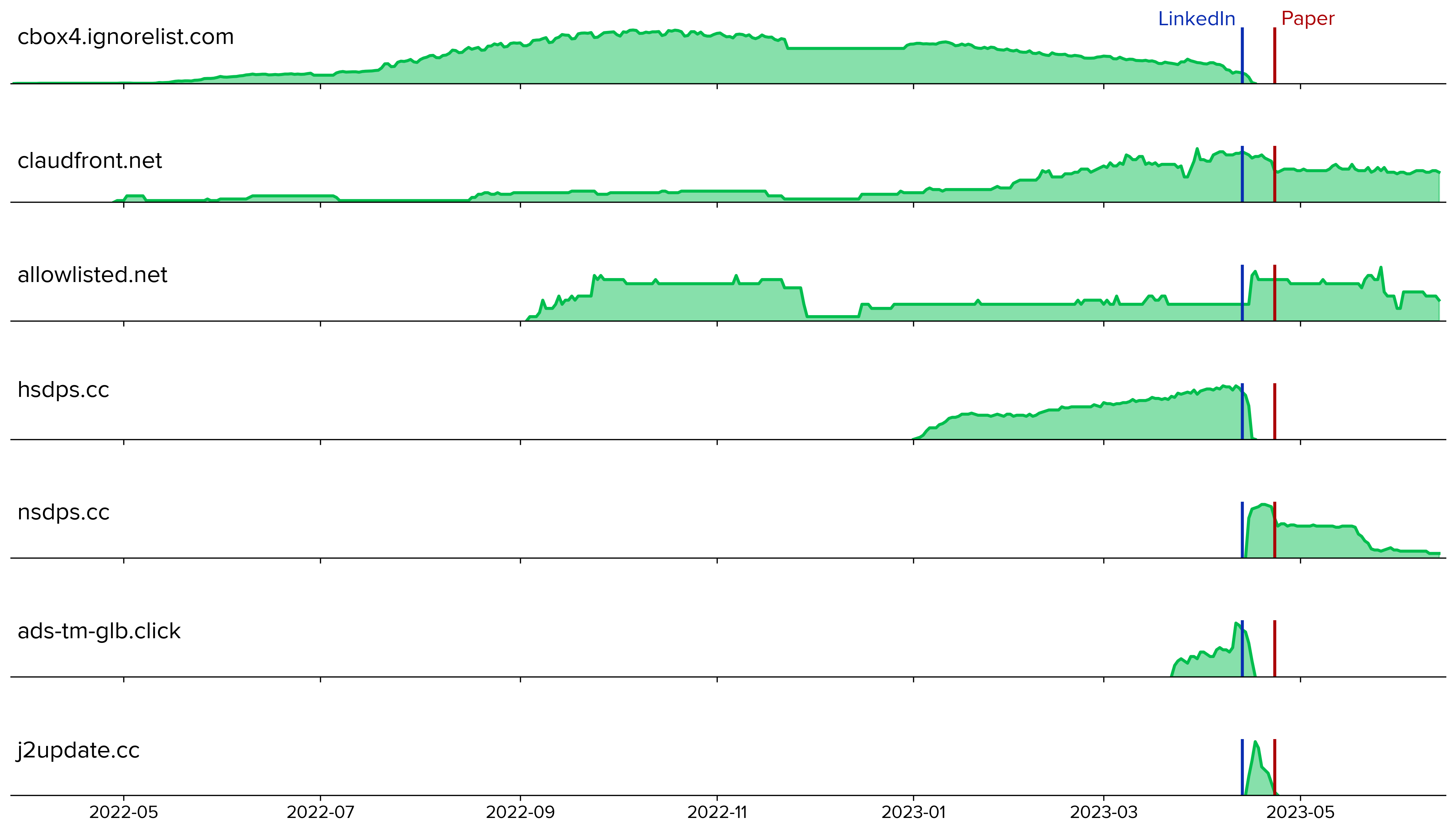
Figure 2. The number of active clients for some of the most active Decoy Dog controller domains over time; note the changes following Infoblox’s disclosure on LinkedIn (blue line) and our release of the full paper (red line). Vertical axes between controllers are not to scale.
Pupy and Decoy Dog Inner Workings
Since April, we have continued to investigate how Decoy Dog differed from Pupy. To better understand Pupy, we deployed our own instance of its C2 server on the Internet. With access to its source code and an active C2 server for testing, we were able to deconstruct its DNS communication protocol and analyze how it works. From there we created a number of DNS signatures to detect new Decoy Dog controllers.
Pupy communications use nonces, which are numbers that are initially randomly generated, to identify sessions with clients and establish the ordering of messages. Decoy Dog uses the same query structure, which allows us to decode the nonce values and correlate different queries to the same compromised device. From there, we were able to track the activity within each controller, including the length of sessions and the number of active clients.
While the use of encryption prevents us from seeing the specific data that is communicated, we have been able to identify the types of messages sent and profile the overall communication behavior of Pupy and Decoy Dog clients. For example, most of the communications traffic is related to exchanging keys to create sessions and then maintaining those sessions. Based on our observations, Decoy Dog traffic includes disproportionately more error messages than Pupy traffic. Some of the queries that resulted in an error response are consistent with third party scanning and not legitimate client queries, most of which occurred after our disclosure.
Perhaps the most surprising difference between the two was highlighted in our original paper: Decoy Dog responds to replays and Pupy does not. In fact, Decoy Dog controllers answer any well-formed request, creating a DNS wildcard-type behavior. One would expect that limiting responses to valid queries, as Pupy does, would minimize chances of the controller being detected. Given the sophistication of the other changes that were made, this behavior was likely intentional, albeit perplexing.
Decoy Dog also exhibits more variance in message payload length than Pupy, indicating that it has a richer set of commands and responses. These expanded communication options led us to partially reverse engineer Decoy Dog samples found on VirusTotal. From this, we confirmed that Decoy Dog is a major refactor of Pupy with a suite of advanced capabilities that have changed over time. The original Decoy Dog appears to have been modified by a second author with additional methods for ensuring continuity of communications between a victim and controller. Decoy Dog also includes a domain generation algorithm (DGA) that was previously unknown. Finally, it added the ability for clients to execute arbitrary Java code, which is only necessary when the operation cannot risk detection. The approach used to implement these features indicates a level of sophistication and intentionality that is beyond many threat actors.
While Decoy Dog has evolved over time, adding increasingly sophisticated capabilities with each release, security vendor detectors still identify it as Pupy. The true capabilities went undetected, possibly because reverse engineers assumed the binary samples were all the same and so were dissuaded from taking a closer look. Was this a deliberate choice of the developer? We don’t know, but it is yet another mystery in the Decoy Dog story. Infoblox is releasing a new YARA rule to detect Decoy Dog and distinguish it from Pupy.
Next Steps
Infoblox continues to track and investigate Decoy Dog. We are continuously updating our threat detection algorithms based on our findings, and in turn, are detecting new controllers all the time. In the meantime, defenders and other researchers should keep the following in mind:
- The IP addresses present in DNS responses sent to clients are generated using encrypted data. They do not represent real IP addresses. Any meaning these IP addresses may have on a network is purely coincidental.
- The DNS queries have meaningful data, particularly the DNS query names, which can be used to track client communication sessions. However, this requires a sizable log history to be achievable.
- The combination of Decoy Dog controllers responding to wildcard requests and aggressive scanning by security vendors can give the false impression that a device has been compromised. If suspicious traffic is observed, the first task should be to verify that the traffic is not a replay.
The story of Decoy Dog reveals an inherent weakness of the malware-centric intelligence ecosystem that dominates the security industry. DNS detection and response is currently the best way of defending against Decoy Dog and may remain so even after victim vulnerabilities and Decoy Dog itself are fully understood. DNS can be used to block access to malicious resources independent of the operating system or application being attacked, and prior to malware discovery.
In order to aid others as they investigate Decoy Dog, we are providing Decoy Dog indicators, traffic logs from our Pupy lab controller, artifacts resulting from our reverse engineering of Decoy Dog clients, and a YARA rule that detects Decoy Dog in our public GitHub repository, which can be found at the URL below.
https://github.com/infobloxopen/threat-intelligence