Author: Nick Sundvall
Overview
On 12 August, Infoblox observed a malspam campaign distributing the Danabot banking trojan through ZIP files.
Customer Impact
First seen by Proofpoint in 2018, Danabot is a banking trojan written in Delphi.1 Danabot can steal credentials, take screenshots, log keystrokes, exfiltrate data to command and control servers (C&Cs), and perform web injection to manipulate browser sessions and steal banking information.2
Campaign Analysis
Some emails in this campaign have empty bodies, and others contain a reference to a seemingly random number, such as № 7585203. The emails’ subject line of “Study the report very urgently” attempts to coerce a recipient into opening the attached file 12.08 – Reports.zip. This ZIP contains a malicious JavaScript file 12.08 – Reports.js, which is filled with shell code.
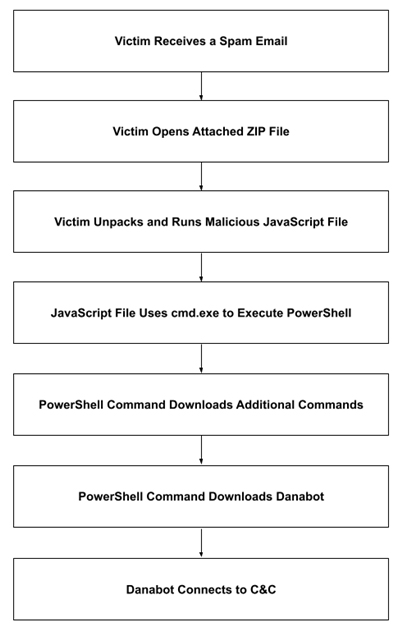
Attack Chain
Opening 12.08 – Reports.zip extracts the malicious JavaScript file. When run, it executes a shell command that runs a PowerShell script with a base64-encoded command. The decoded command downloads an additional PowerShell command, which downloads and executes the final payload, Danabot. From here, Danabot connects to its C&C, and can exfiltrate data and receive additional commands.
Vulnerabilities & Mitigation
Because malspam emails are a common distribution method for malicious scams, Infoblox recommends the following precautions typically used to avoid these attacks:
- Always be suspicious of vague or empty emails, especially those that contain prompts to open attachments or click links.
- Be aware of an attachment’s file type, and never open an attachment that could be a script (.js, .vbs, .cmd, or .bat), an internet shortcut file, or a compressed file. Threat actors use compressed files to evade detection methods that are based on file hashes and signatures. They also use compressed files to mask the real malicious files that would be flagged by email services.
- Verify the legitimacy of emails with the alleged sender before opening any attachments.
Endnotes
- https://www.proofpoint.com/us/threat-insight/post/danabot-new-banking-trojan-surfaces-down-under-0
- https://www.proofpoint.com/us/blog/threat-insight/new-year-new-version-danabot