Author: Nathan Toporek
TLP: WHITE
Overview
On May 21 Infoblox observed a malicious spam campaign delivering Graftor malware via malicious file attachments. The threat actor(s) used a generic Invoice theme to lure victims into opening a weaponized Excel Spreadsheet.
Customer Impact
Graftor, a.k.a LoadMoney, is a family of adware that has been used by threat actors for more than nine years.1 Once a victim is infected, it will install unwanted software on their machine.
While our samples no longer fully executed, past versions of Graftor were capable of browser hijacking, injecting advertising banners, installing other unwanted applications, changing a user’s homepage and search provider, and launching other adware. They also had anti-detection capabilities such as antivirus and sandbox detection.2
Campaign Analysis
Over the years, threat actors have distributed Graftor via malicious spam emails, as well as via free software (freeware) installers.3
In this campaign, threat actor(s) used a subject line of RE:Fwd: REQUOTE PENDING ORDER to lure victims to open the email. Individual messages were empty, but all emails had a malicious attachment named INVOCE#4587.xlsx.
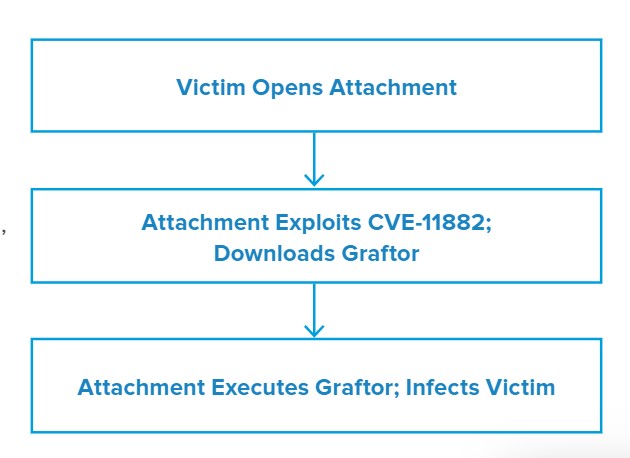
Attack Chain
When the victim opens the file attachment it will exploit CVE-11882 to download and execute the Graftor binary.
Vulnerabilities & Mitigation
This campaign relies on both social engineering tactics and software exploits to infect victims with Graftor malware. As such, Infoblox recommends the following precautions:
- Keep computers and all endpoints up-to-date with the latest security patches to block known vulnerabilities that could be targeted by threat actors.
- Regularly train users about potential phishes and how to handle them appropriately.
- Implement attachment filtering to reduce the likelihood of malicious content reaching a user’s workstation.
- Do not open attachments that are unexpected or from unfamiliar senders.
Endnotes
- https://hotforsecurity.bitdefender.com/blog/adware-shifts-focus-from-advertising-to-data-harvesting-2942.html
- https://blog.talosintelligence.com/2017/09/graftor-but-i-never-asked-for-this.html
- https://blog.talosintelligence.com/2017/09/graftor-but-i-never-asked-for-this.html