Author: Avinash Shende
1. Overview
On 24 September, Infoblox observed a malicious email campaign distributing the remote access trojan (RAT) AsyncRAT, which has also been used in ongoing cyberattacks on the aviation industry.1 AsyncRAT is being propagated via a weaponized executable attached to emails made to appear to be coming from DHL.
AsyncRAT, also known as RevengeRAT, is designed to remotely monitor and control an infected computer through a secure, encrypted connection. It can be dropped by other malware, downloaded, or received as an email attachment.
2. Customer impact
Cyber criminals use AsyncRAT to log keystrokes, install ransomware and trojans, monitor an infected machine and manage its files, and steal sensitive personal and financial information. AsyncRAT is powerful enough to steal a victim’s identity and cause financial loss.
3. Campaign analysis
Emails in this campaign are designed to appear to come from support@dhl[.]com, have no body, and contain an attachment: a RAR file called Consignment Documents.rar. The From name in the emails is DHL EXPRESS, and the subject line is Consignment Notification: You Have A Package With Us.
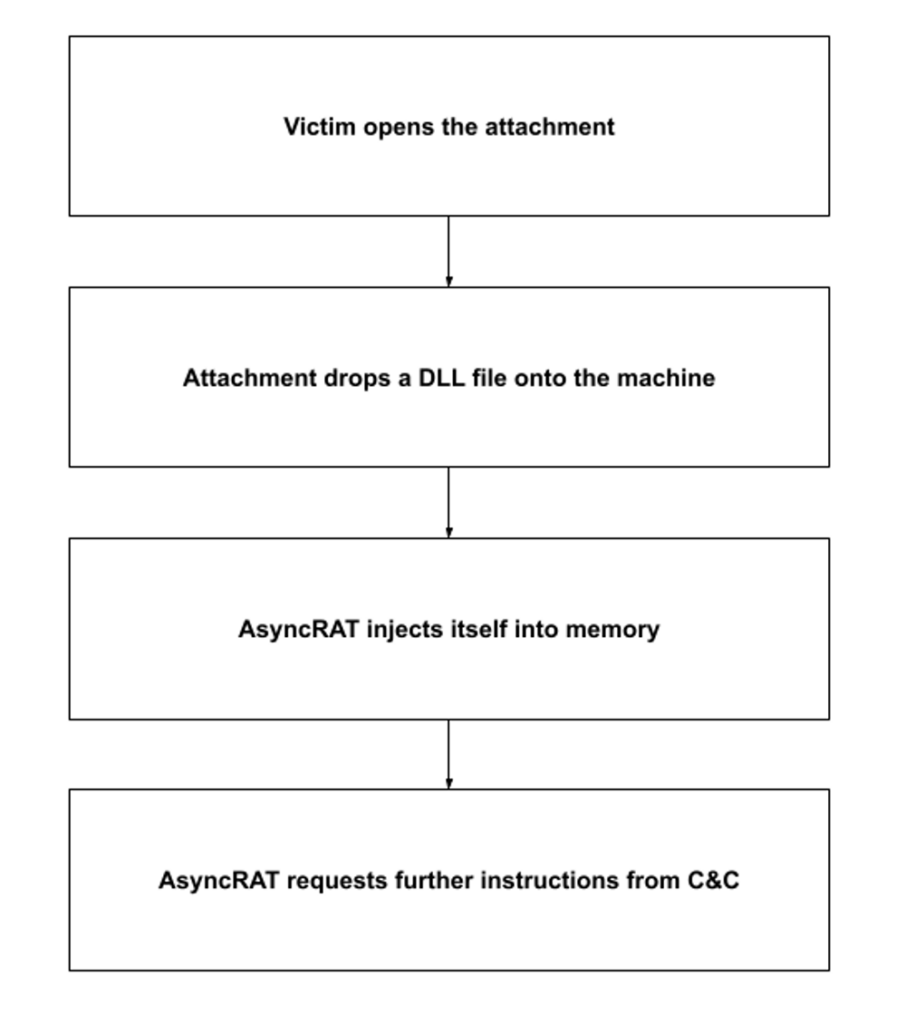
4. Attack chain
Upon execution, AsyncRAT tries to detect sandboxes and other dynamic analysis tools on a victim’s machine. It then drops tgrwreswfky.dll, a malicious DLL file used to modify and delete registry keys, to c:\Users\user\AppData\Local\Temp\nst613E.tmp\. It then creates a new process and injects itself into the process running in memory. The new process then tries to establish communication with its command and control (C&C) server and requests further instructions from the threat actor.
5. Vulnerabilities and mitigation
Infoblox recommends the following actions for reducing the risk of infection by AsyncRAT:
- Keep antivirus signatures and engines up to date.
- Turn on automatic updates, to keep the operating system up to date with the latest security patches.
- Do not expose email addresses to the internet.
- Do not open email attachments with extensions that look unfamiliar.
- Exercise caution when opening all email attachments, especially those that come from unfamiliar senders.
- Avoid opening emails with generic subject lines.